Technology has been playing a critical role in our lives for decades. From hand-held Pagers to giant Walkie-Talkies to Smartphones, the impact on our lives by these gadgets has been fantastic. The more we use technology, the more data we produce and the more effort it takes to handle the data and store it.
ALSO READ: What Is An eSIM? How Is It Better Than A Standard SIM Card? [Explained]
Tracking Your Online Activity
Have you ever wondered why the beautiful dress that you recently searched for on an Online shopping website appears on other sites in the form of ads? Is it just a coincidence or a magical spell? It’s neither of that, sadly.
The moment you search for a product online, your browsing behavioral data gets collected by these companies, and the ads get displayed on other sites that you browse. This process is also known as “Behavioural Targeting,” and this happens to every internet user out there surfing.

Now, does this mean your privacy is at risk? The short answer is, Yes. Your data is being collected and sold at higher prices while you are still searching for the perfect dress to wear at the party. Privacy has become a massive concern as the internet is expanding.

People tend to store their e-mails, password, and other personal information without knowing that it is being compromised and sold. There are many ways of browsing securely, and one of them is by using Tor.
What Is Tor?
Tor is a non-profit firm that researches on anonymity and privacy of internet users. The name is derived from an acronym for the original software project name “The Onion Router”. Tor’s intended use is to protect the personal privacy of its users, as well as their freedom and ability to conduct confidential communication by keeping their Internet activities unmonitored. It is free to download like any browser and is available for Windows, Mac, Android, and iOS.

When you use the internet, be it from your browser or your smartphone, your ISP (Internet Service Provider) and other elements can track and access your search history, even in Incognito mode or Private window that Chrome and Firefox offers. It always has an eye on you about which websites you visit. The only way out is to hide your identity, but how do you do that? Here’s where Tor shines.
ALSO READ: What Is VPN And Why You Must Use It? [Explained]
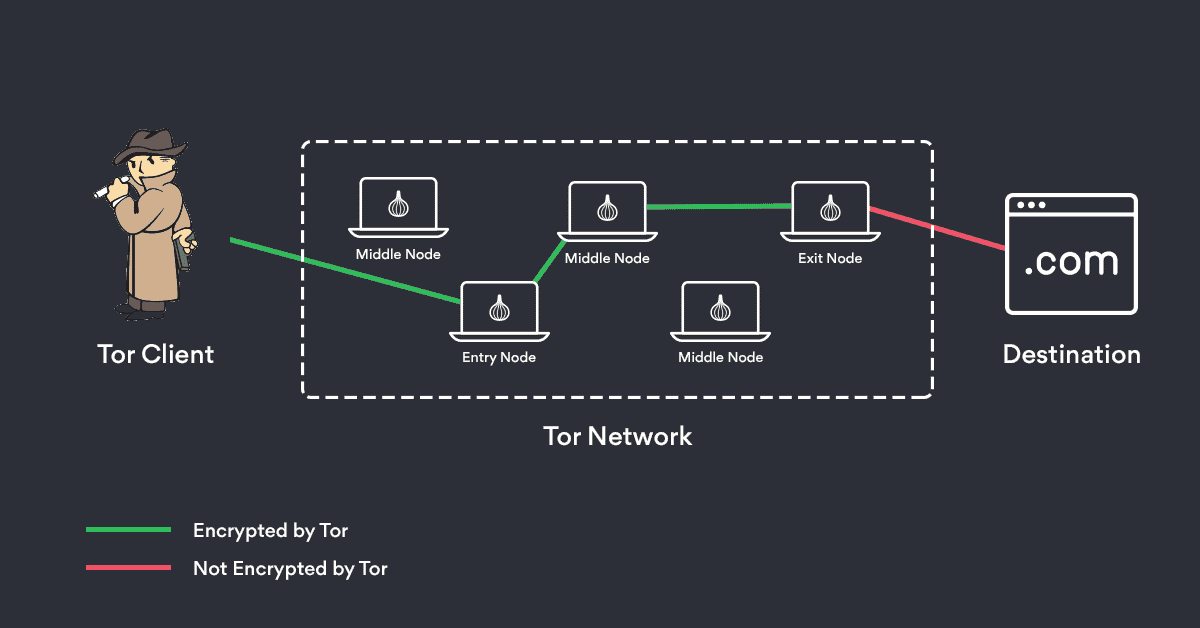
Tor uses technology that bounces internet users, pretty similar to Blockchain, except it hides the user info. When you use Tor, you get connected to the “Nodes” in different locations around the globe. The connection is secured using end-to-end encryption among the connected “Nodes.”
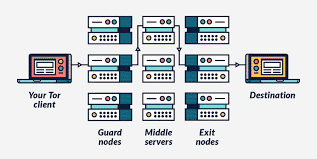
What are the Nodes? These are Tor servers distributed across the globe, and encryption ensures that your identity is hidden. Let us say you wish to speak up against the government. Tor can get it done for you without any fear of getting caught. When the officials try to look for you, they will get redirected to the location of the server from where the data was sent. So, they’ll never figure out your exact location.
Every good comes with a tradeoff. Here in the case of Tor, you might get stuck in an endless loop of captchas, or websites might send back 404 errors. The browsing experience will be slower than usual due to the requests that the browser has to send between nodes to get the data. Overall, there are high chances of a poor browsing experience.
History Behind Tor
The US navy developed tor in 2002, and it has received 60% of funds from the Department of Defence. At first, the main goal was to protect the user’s privacy from corporations rather than governments, and it has come a long way since then. People concerned about their privacy, and even black hat hackers use Tor.

Tor gives users passage to Dark Web, where a lot of undiscovered websites become accessible. There’s a lot on Dark Web, which we don’t know (or probably won’t come across), and therefore in some provinces, it is a crime to use Dark Web.
ALSO READ: Privacy And Data Protection: Who Is Responsible? [TDAnalysis]
You might ask why Tor still exists after the dark side that it has got. The answer is, because of the people who use it. Even though organizations and governments know it’s illegal to access the private data of people, they do and sell it, and consequently, people have got a good reason to debate on the same.

Admittedly, we are the only ones who can guard our privacy from organizations trying to make money by selling it. As the owners of our data, we have every right to protect our privacy. It is entirely legal across the globe to use Tor, and we don’t see any reason why you shouldn’t use it if you have grave concerns about privacy.
Written by Mohammed Abubakar (intern), edited by Atish Rajasekharan
BONUS VIDEO
For the latest tech news, follow TechDipper on Twitter, Facebook, Telegram, Instagram, and subscribe to our YouTube channel.


![Wifi 6 - Wi-Fi 6 And Wi-Fi 6E: Everything You Need To Know [Explained] Wi-Fi 6](https://techdipper.com/wp-content/uploads/2020/05/Wifi-6-400x200.jpg)